SleekView for Google Authenticator
Google Authenticator writes the TOTP secret, the enrolment timestamp, and the recovery-code state to per-user meta. SleekView reads those meta rows and renders the user base as a sortable, filterable enrolment grid you can actually audit.
♾️ Lifetime License available
2FA coverage that survives the profile screen that produced it
Google Authenticator does the cryptographic work well. Each enrolled account picks up a TOTP secret, an enrolment timestamp, a recovery-code counter, and a boolean enrolment flag, all written to per-user meta. The user list screen carries a column that tells you whether a specific account has 2FA on, which is the right surface for one user and the wrong surface for asking whether the administrator role meets the policy threshold.
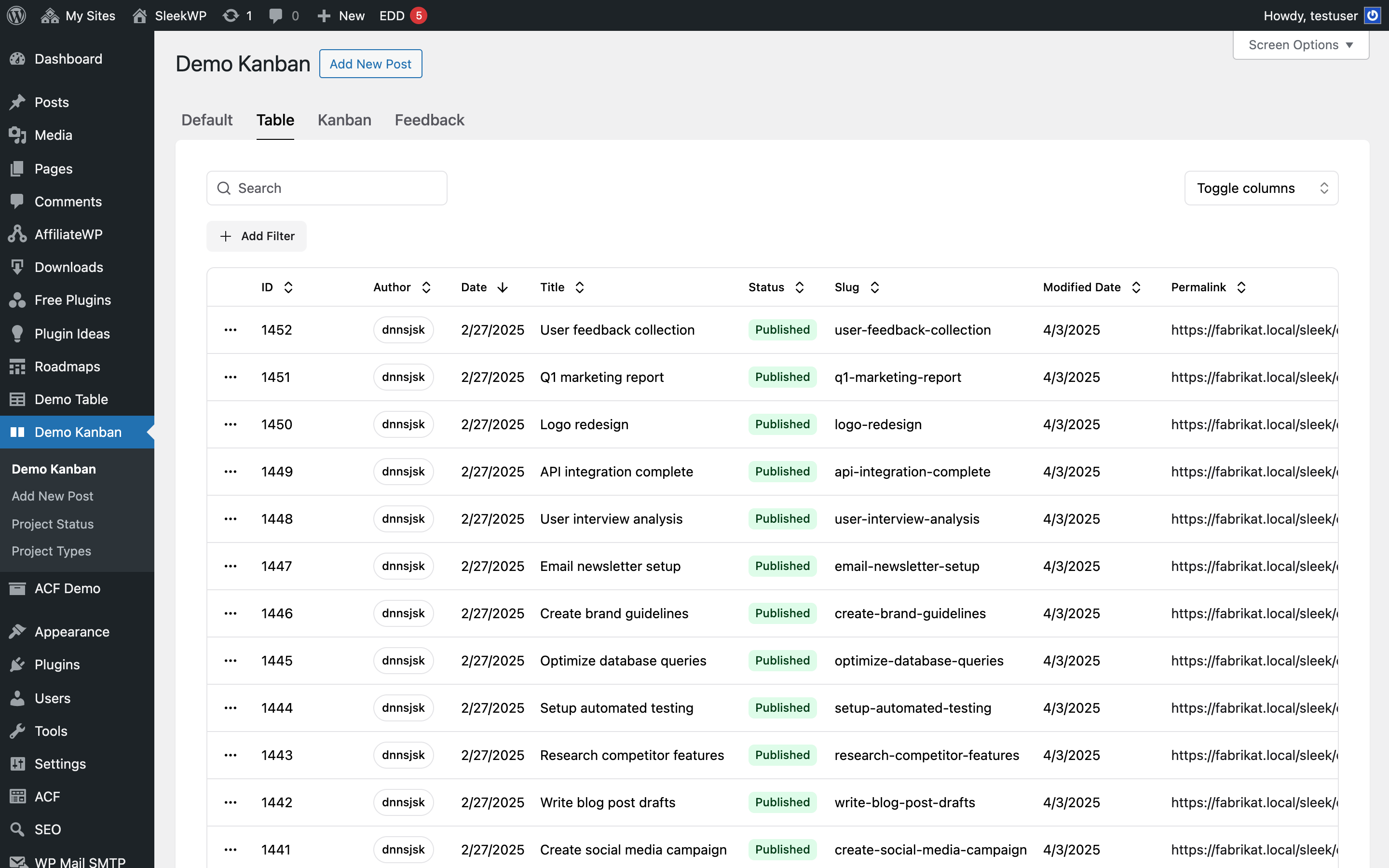
SleekView reads the same user meta keys the plugin maintains and joins them to wp_users. Each row carries the username, the role, the enrolment status, the enrolment date, the recovery-codes-used count, and the last-login timestamp. A row showing role Administrator and enrolment Inactive next to a last-login of yesterday gives the security lead exactly the picture the user list screen does not summarise on a Monday morning.
Saved filters earn their keep here. A view filtered to role equals Administrator and status equals Inactive becomes the policy-compliance check. A view filtered to recovery-codes-used greater than five isolates the accounts that have probably lost their device. The plugin keeps writing exactly what it always wrote; SleekView turns it into a real operational surface.
Workflow
From per-user meta to a real 2FA grid
Read the 2FA user meta
Map the columns
Save the coverage check
Drill into the account
Sample columns
2FA enrolment across the user base
wp_usermeta keys written by Google Authenticator joined to wp_users
| User | Role | Status | Enrolled | Codes used | Last login |
|---|---|---|---|---|---|
| dennis | Administrator | Active | 2025-11-04 | 0 | 2026-05-15 |
| claire | Administrator | Inactive | — | — | 2026-05-15 |
| marco | Editor | Active | 2026-01-12 | 3 | 2026-05-14 |
| aiko | Editor | Pending | 2026-05-10 | 0 | 2026-05-13 |
| lena | Subscriber | Inactive | — | — | 2026-04-29 |
Comparison
Default Google Authenticator admin vs SleekView
Default Google Authenticator
- User list shows a 2FA column but does not aggregate it
- No saved filter for inactive administrators
- Recovery-code usage sits inside the user profile, not the list
- Role-by-role coverage requires a manual user-list scan
- Last-login context is not joined to the enrolment column
SleekView
- One row per user with role, status, and enrolment date
- Filter by role and enrolment status in one click
- Saved view for inactive administrators
- Spot accounts with high recovery-code consumption
- Click through to the profile or the wp_usermeta row
Features
What SleekView gives you for Google Authenticator
Policy coverage as a grid
Filter to role equals Administrator and status equals Inactive to see exactly which privileged accounts still need to enrol. The view becomes the policy-compliance check the user list cannot summarise.
Recovery-code triage
Sort by codes used to surface accounts that have probably lost their device. A user with five of eight codes burned is a re-enrolment prompt, not another recovery code.
Audit-ready exports
Export any filtered slice to CSV with active filters preserved. SOC and ISO evidence requests for 2FA coverage become a one-click operation instead of a manual spreadsheet.
Audience
Who uses SleekView for Google Authenticator
Security leads
One sortable grid answers 'which administrators still need 2FA?' without scrolling the user list. The view replaces the quarterly CSV export most security reviews still rely on.
Compliance owners
Per-role enrolment totals filterable to the exact slice an auditor asks for. The chart export answers SOC and ISO control evidence questions without engineering involvement.
IT ops
Recovery-code consumption sortable on one screen surfaces accounts heading toward a silent lockout. The grid turns the wp_usermeta rows into a working triage list.
The bigger picture
Why 2FA enrolment needs a workspace, not a column
Google Authenticator is well scoped for what it owns: generating, storing, and verifying TOTP secrets per user. The hard part for security teams is not the cryptography but the operational view. Knowing the enrolment rate across roles, which administrators still need to enrol, and which accounts have burned through their recovery codes matters more on a Monday morning than the underlying algorithm.
None of those questions get answered from the per-user profile screen the plugin ships with, and the small 2FA column on the user list is honest but not aggregated. SleekView reads the same user meta keys and lays a real grid over them. Same secrets, same recovery-code counters, much better posture for the team relying on them.
Questions
Common questions about SleekView for Google Authenticator
No. The view reads only the enrolment flag, the timestamp, the role association, and the recovery-code counter. The TOTP secret itself never leaves the user meta row, which keeps the grid compatible with the plugin's security model.
From the user meta keys Google Authenticator writes per account, joined to wp_users for role, username, and last-login. No additional logger and no premium add-on is required on the Authenticator side.
Yes. The role column is filterable, so isolating administrators, editors, or any custom role is one click. A view scoped to administrators-only is the standard policy-compliance check most security teams run weekly.
Yes. The premium tier adds policy enforcement and app-password support but stores the same enrolment state in user meta. SleekView reads whatever fields are present, so premium-only metadata appears as additional columns when the view is rebuilt.
Yes. Sort the grid by codes used to find the accounts that have burned through most of their recovery codes. A user with five of eight codes consumed is usually a lost-device situation worth a re-enrolment prompt before it becomes a support ticket.
Yes. The plugin writes per-site user meta where applicable, and SleekView respects that scope. On multisite each subsite has its own enrolment grid, and a network-level view can roll users up across blogs when one security team monitors the whole network.
No. Only the rows on the current page are queried, and user meta lookups use the indexed user_id column. A site with tens of thousands of accounts queries the same as a site with a hundred because pagination keeps the row count constant.
Yes. Any filtered view exports to CSV with active filters preserved. Quarterly security reviews and SOC evidence packs get a defensible sheet instead of a screenshot of the user list with the 2FA column highlighted.
Pricing
More than 1000+
happy customers
Explore our flexible licensing options tailored to your needs. Upgrade your license anytime to access more features, or opt for a lifetime license for ongoing value, including lifetime updates and lifetime support. Our hassle-free upgrade process ensures that our platform can grow with you, starting from whichever plan you choose.
Lifetime ♾️
Most popular
EUR
once
- Unlimited websites
- Lifetime updates
- Lifetime support
...or get the Bundle Deal
and save €250 🎁
The Bundle (unlimited sites)
Pay once, own it forever
Elevate your WordPress site with our exclusive plugin bundle that includes all of our premium plugins in one package. Enjoy lifetime updates and lifetime support. Save significantly compared to buying plugins individually.
What’s included
-
SleekAI
-
SleekByte
-
SleekMotion
-
SleekPixel
-
SleekRank
-
SleekView
€749
Continue to checkout